In today’s digital landscape, information security has become a top priority for organizations of all sizes. With the increase in cyber threats and the need to comply with regulations, businesses are establishing dedicated teams to ensure the effectiveness of their information security programs. One such team is the Information Security Governance, Risk, and Compliance (GRC)
In the rapidly evolving realm of IT, businesses are faced with a multitude of options when it comes to managing their data and applications. The choices can be broadly categorized into on-premise servers, public cloud services, private cloud solutions, and hybrid cloud models. Each option has its own advantages and considerations, making it crucial for
In today’s digital landscape, where cyber threats are constantly evolving, it is imperative for organizations to prioritize the protection of their digital assets. Vulnerability Assessment and Penetration Testing (VAPT) is a comprehensive security testing approach that plays a crucial role in identifying and addressing cyber security vulnerabilities. By combining vulnerability assessment and penetration testing, VAPT
In today’s evolving threat landscape, relying solely on network firewalls is no longer sufficient. Once an attacker breaches the perimeter, traditional security models often offer little resistance. The long-held assumption that everything inside the network can be trusted simply no longer applies. With remote work, cloud applications, third-party integrations, and distributed teams now the norm,
Operational efficiency today depends on more than just robust infrastructure — it relies equally on skilled people, structured processes, and responsive support models. As enterprises scale, manage distributed environments, and adopt digital-first operations, the need for reliable Facilities Management Services (FMS) and flexible staff augmentation solutions has never been greater. At CoreGenix, we deliver structured
In 2026, enterprises can no longer afford network gaps that impact uptime, productivity, or security. As digital operations expand across cloud, data centres, and hybrid environments, network performance has become a critical business enabler rather than a background IT function. Studies indicate that nearly 40% of outages and performance issues are preventable, often caused by
After completing more than 100 security audits this year, one reality has become clear: most organisations are not as secure as they believe. Despite investments in tools and technologies, fundamental security gaps continue to expose enterprises to preventable risks. Weak identity controls, outdated endpoints, misconfigured firewalls, and limited visibility remain some of the most common
Artificial Intelligence is rapidly transforming cybersecurity. From faster threat detection to automated response, AI-driven tools are helping organisations strengthen defences against increasingly sophisticated attacks. However, AI in cybersecurity is not without challenges. Alongside the benefits come new risks—adversarial attacks, data bias, false positives, and opaque decision-making—that can impact security operations if left unchecked. As enterprises
Operational Technology (OT) environments are now prime targets for advanced cyberattacks. As industrial systems become increasingly connected, cyber incidents no longer impact only IT systems—they directly affect production, safety, uptime, and revenue. From manufacturing plants and utilities to critical infrastructure, OT assets such as ICS, SCADA, and PLC environments require security strategies that are purpose-built
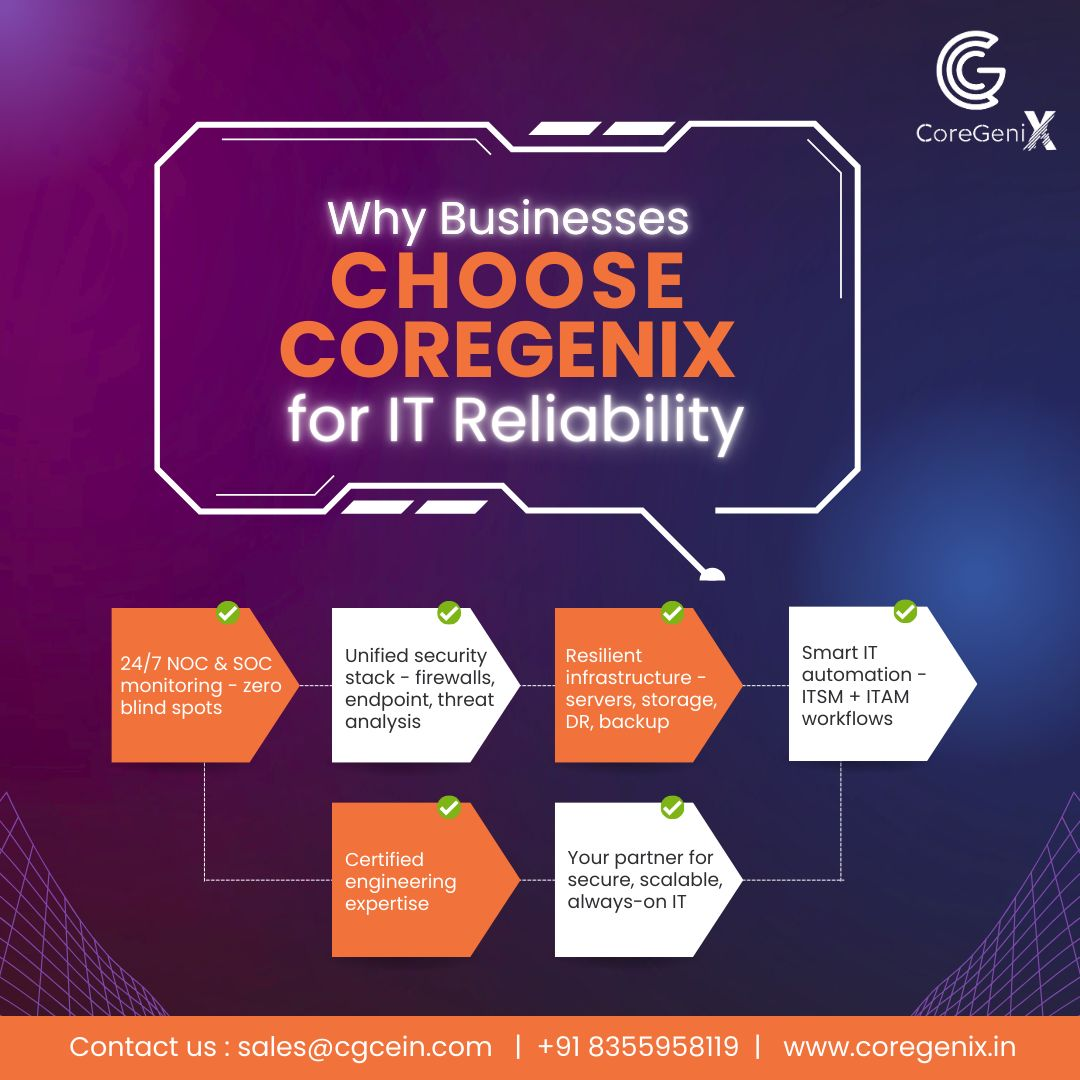
In today’s enterprise landscape, downtime is no longer an option. Digital operations, distributed teams, and customer-facing platforms demand uninterrupted availability. This is where Always-On IT becomes a critical business requirement rather than just an IT objective. Every minute of downtime impacts productivity, revenue, and customer trust. For organisations competing in 2026 and beyond, IT reliability