Operational Technology (OT) environments are now prime targets for advanced cyberattacks. As industrial systems become increasingly connected, cyber incidents no longer impact only IT systems—they directly affect production, safety, uptime, and revenue. From manufacturing plants and utilities to critical infrastructure, OT assets such as ICS, SCADA, and PLC environments require security strategies that are purpose-built
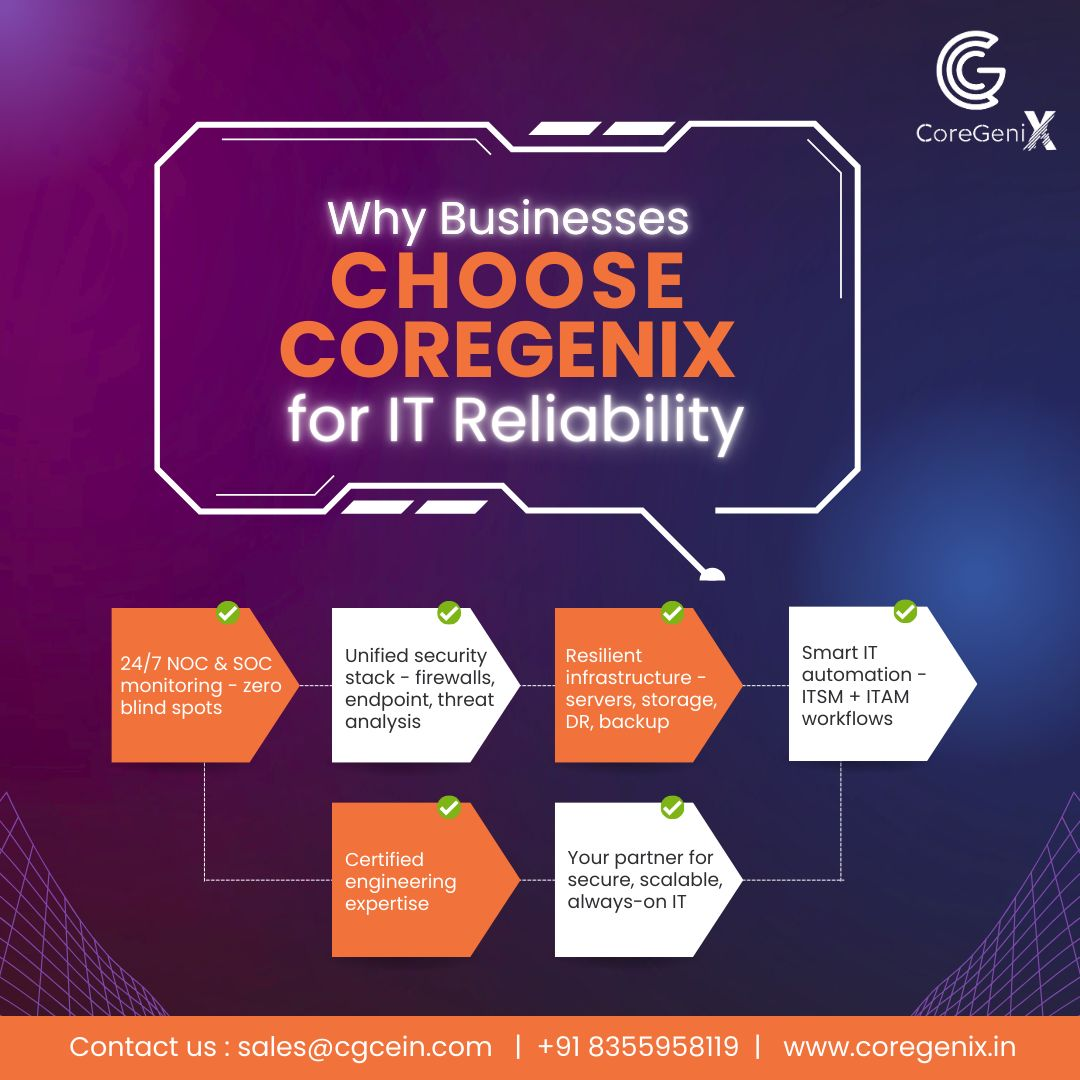
In today’s enterprise landscape, downtime is no longer an option. Digital operations, distributed teams, and customer-facing platforms demand uninterrupted availability. This is where Always-On IT becomes a critical business requirement rather than just an IT objective. Every minute of downtime impacts productivity, revenue, and customer trust. For organisations competing in 2026 and beyond, IT reliability
As organisations prepare for 2026, IT infrastructure is no longer just a support function—it is a strategic business enabler. CIOs are under increasing pressure to ensure that networks, security, cloud platforms, and automation are resilient, scalable, and aligned with long-term business goals. This IT Infrastructure Checklist serves as a practical starting point for building secure,
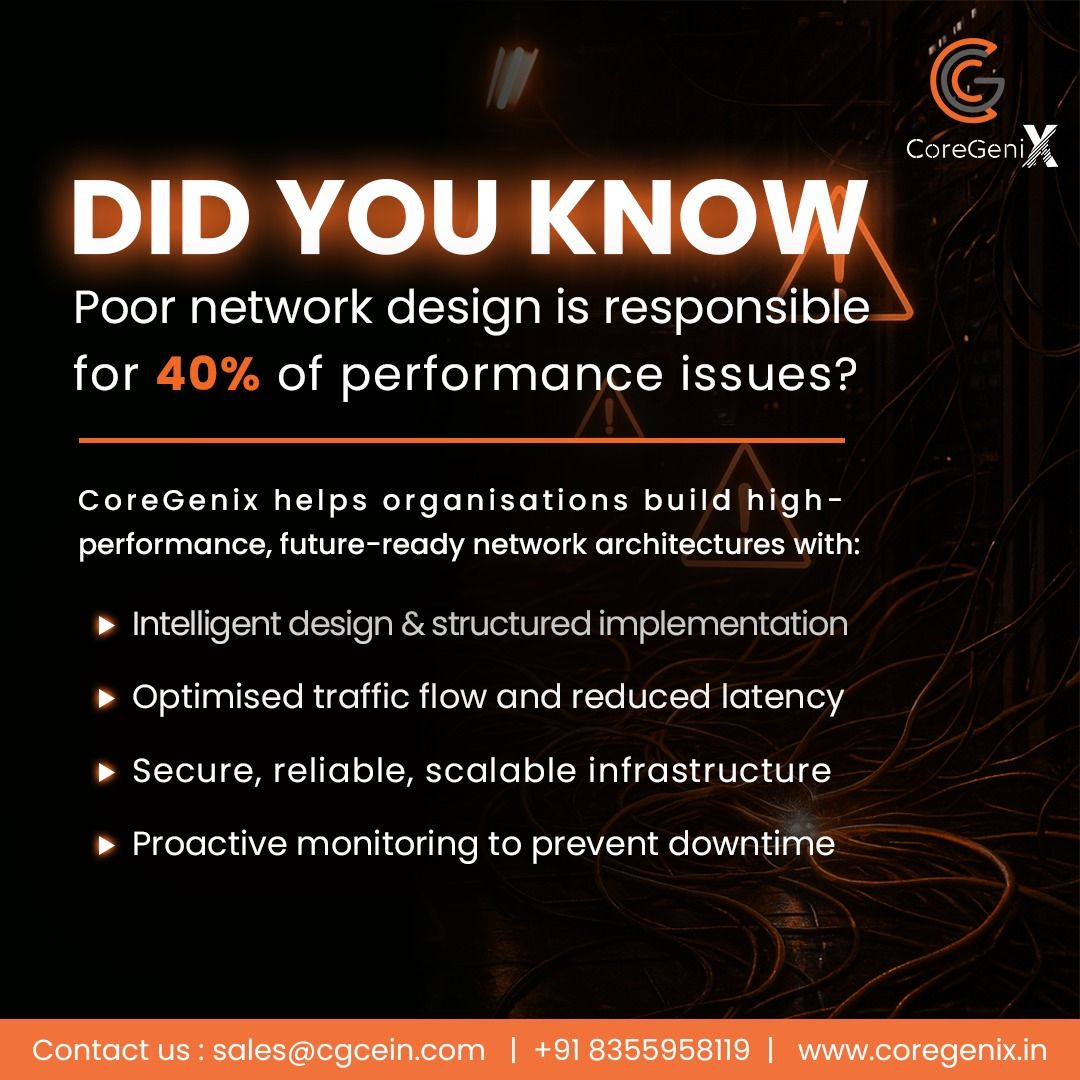
Did you know that poor network design is responsible for nearly 40% of performance issues in enterprise environments? As organisations scale digital operations, adopt cloud platforms, and support distributed teams, network architecture has become a critical determinant of performance, reliability, and business continuity. When networks are designed without scalability, visibility, or resilience in mind, performance
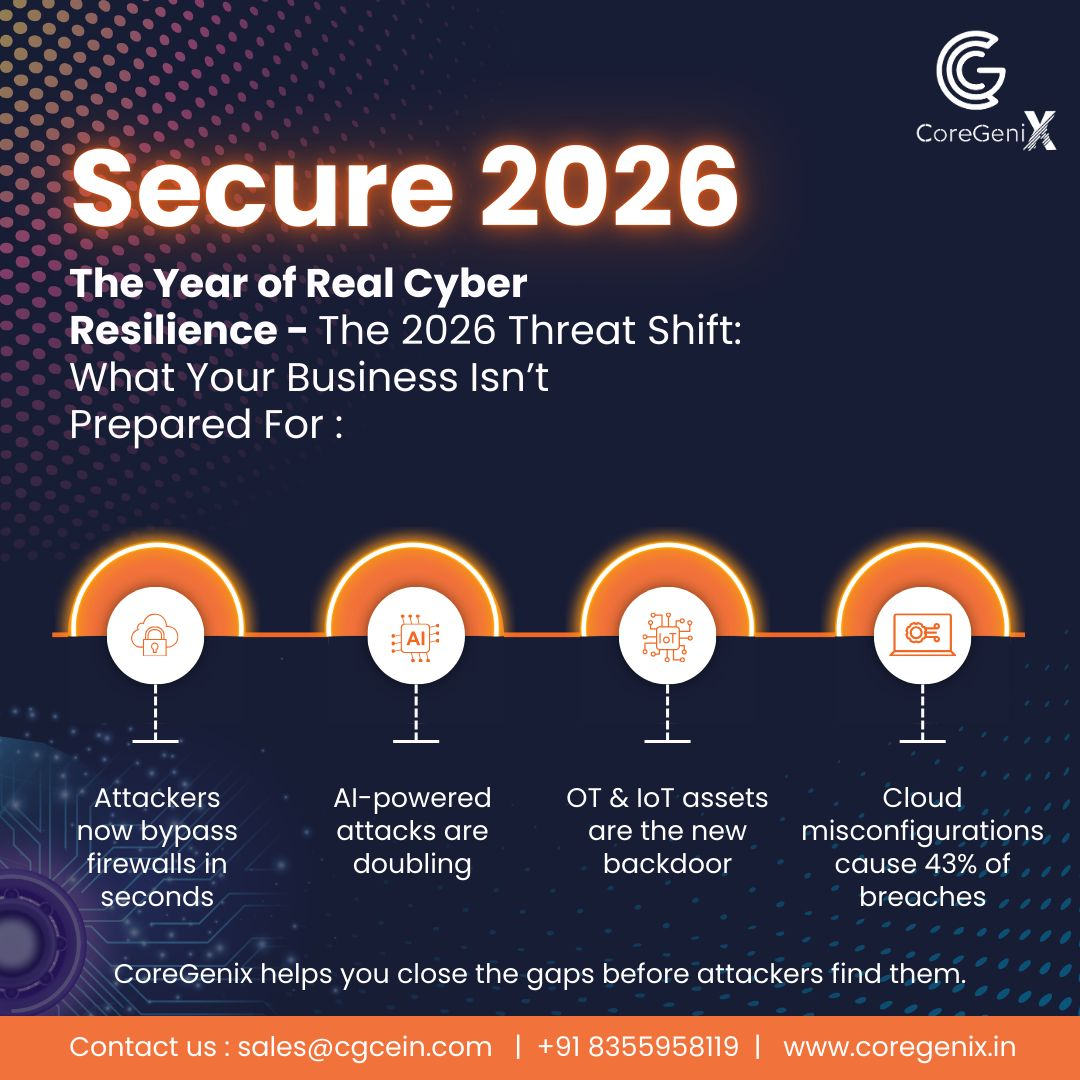
2026 brings a new wave of cyber risks—and most organisations are not fully prepared. The threat landscape has shifted beyond traditional perimeter security, exposing gaps that attackers exploit in seconds. From AI-powered attacks to insecure OT, IoT, and cloud environments, modern enterprises face threats that demand a stronger, more resilient cybersecurity approach. The 2026 Threat
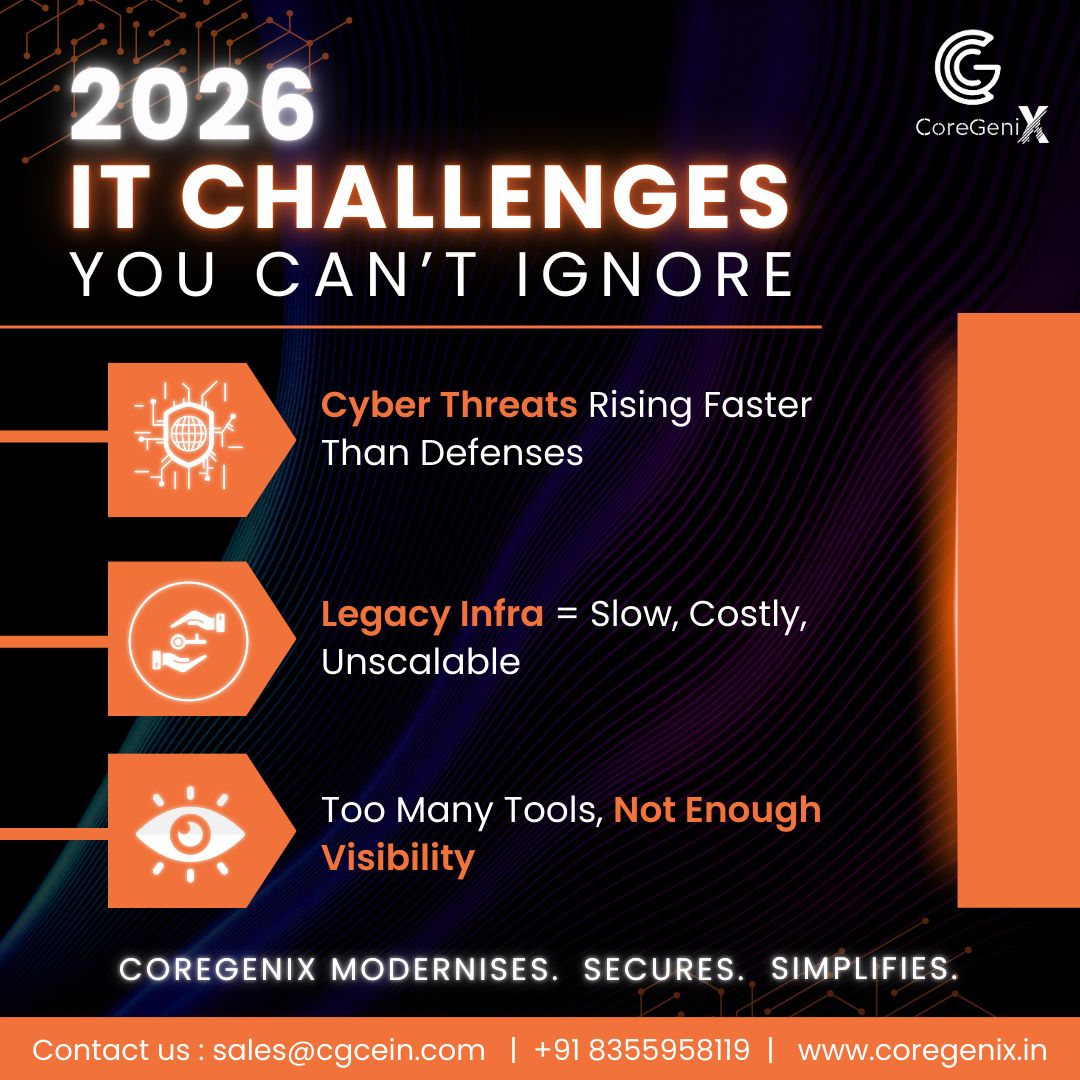
As enterprises move toward 2026, IT leaders are facing a convergence of challenges that can no longer be postponed. Rapid digital expansion, evolving cyber threats, and growing infrastructure complexity are pushing traditional IT models to their limits. Most organisations are entering 2026 with three critical IT challenges: rising cyber threats, outdated infrastructure, and fragmented visibility
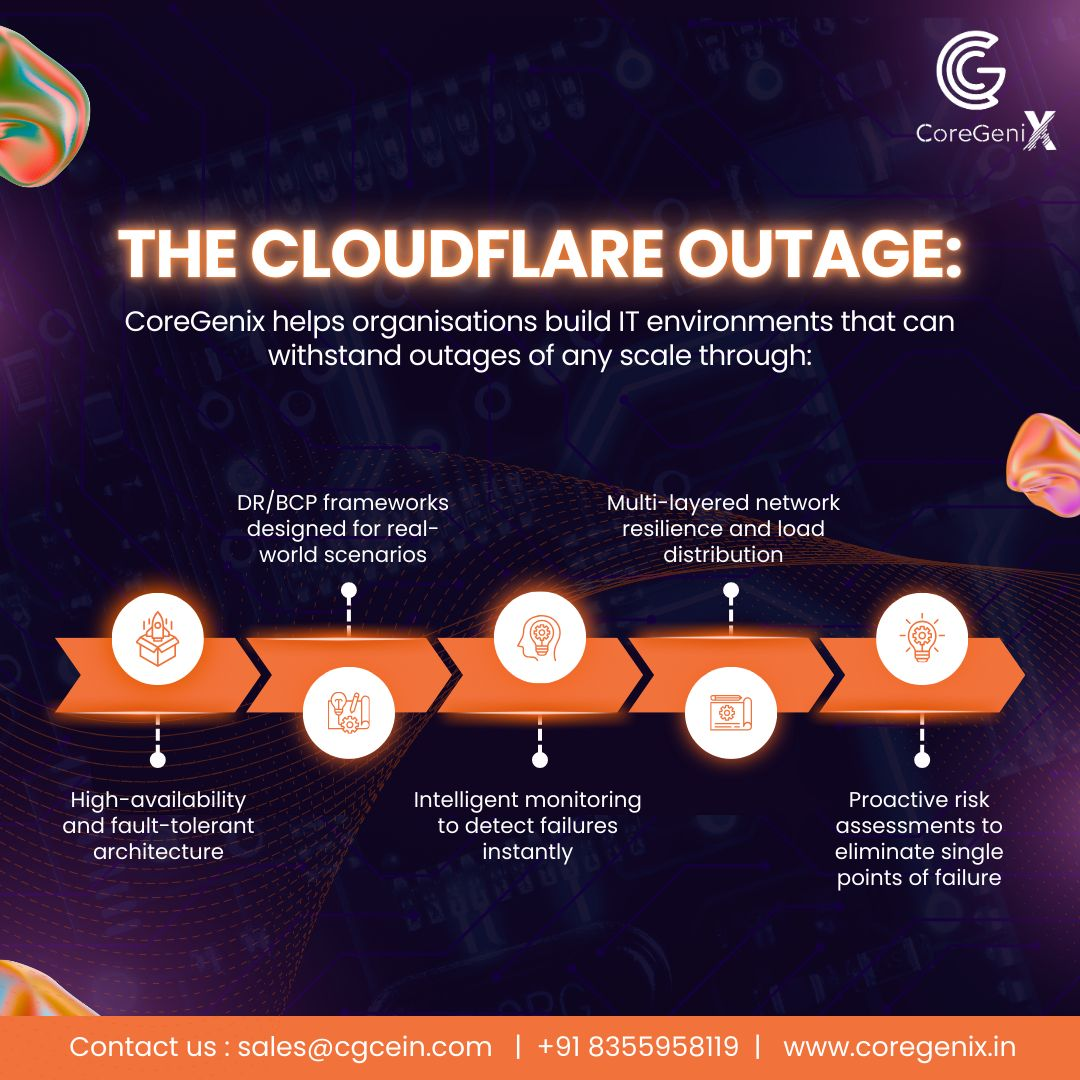
The recent global outage that impacted major platforms, cloud services, and AI-driven tools was more than a temporary disruption—it was a clear warning for every organisation that depends on digital infrastructure to operate. These events reinforced a critical reality: even the strongest technology providers can fail. When they do, your resilience strategy determines whether the
“Never trust, always verify” is a phrase echoed across almost every cybersecurity conversation today. But in real enterprise environments, Zero Trust is not just a framework or a marketing term—it is a fundamental shift in how security is designed, deployed, and sustained. At CoreGenix, we believe Zero Trust must work in the real world, not
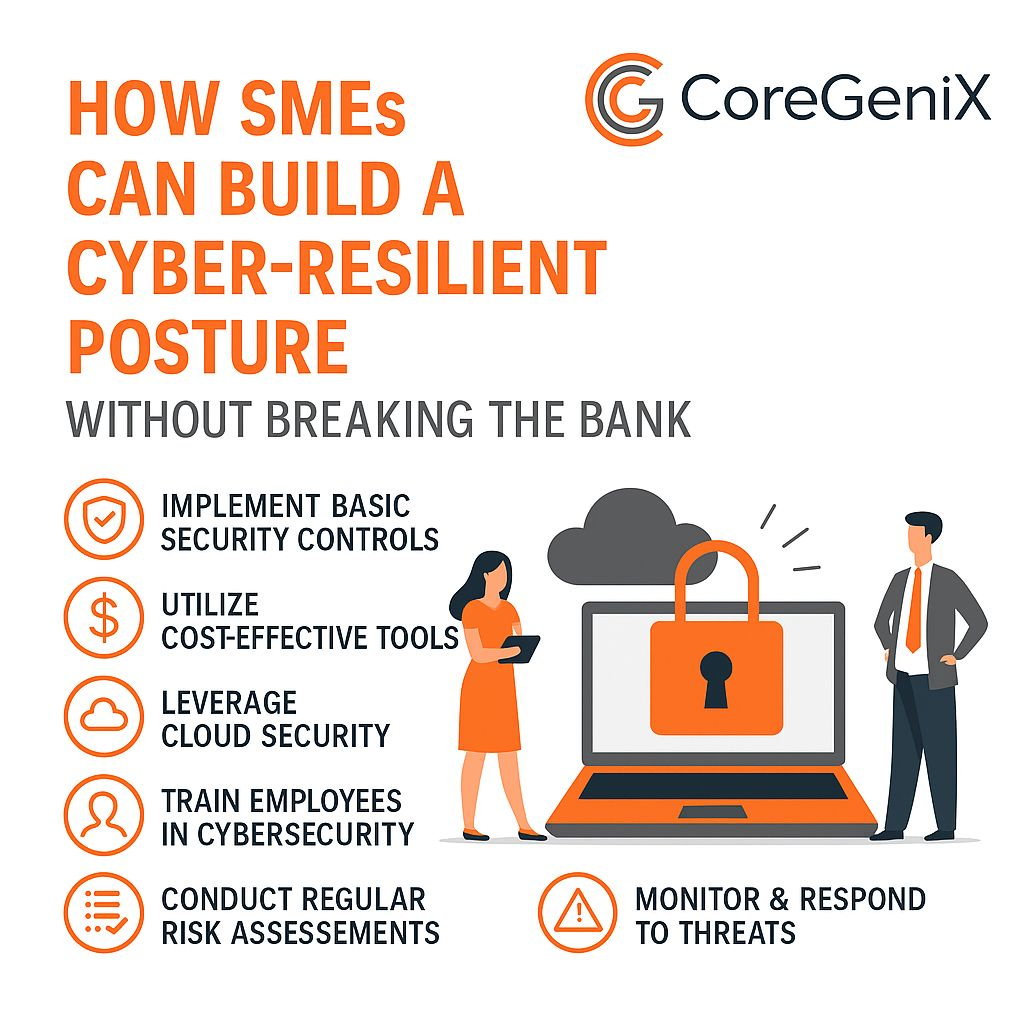
Many small and mid-sized enterprises (SMEs) believe that cybersecurity requires enterprise-grade budgets, complex frameworks, and expensive tools. In reality, most cyber incidents in SME environments don’t happen due to a lack of technology—they happen because of limited visibility, poor prioritisation, and weak continuity planning. Cyber resilience isn’t built on budget. It’s built on clarity, consistency,
In cybersecurity, what you don’t review regularly often becomes your weakest link. Threats evolve constantly, configurations drift, and access permissions change—sometimes without notice. That’s why quarterly security audits are no longer just a compliance activity; they are a core pillar of cyber resilience. At CoreGenix, we’ve consistently observed that organisations conducting structured quarterly control reviews